
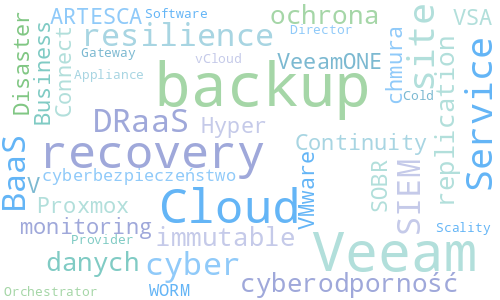
What is an IMMUTABLE backup?
How to make your backups tamper-proof, unalterable, and undeletable — resilient against malware and human error.
We protect digital assets and backup infrastructure against ransomware and human error using a proprietary methodology.
.png)
Over the past decade, we have been building and promoting Backup & Disaster Recovery as a Service for data center operators across Poland. These services operated under a 24/7/365 regime, as hundreds of organizations depended on them for business continuity. Now we bring the same expertise and advanced tools directly to your organization — with full transparency in both the offering and the technology applied.
Uncompromising data security through the combined power of four domains
.png)
Organizations only protect data that is processed in systems known to the IT team. The real challenge lies in unstructured data scattered across local repositories, SaaS applications, and unmanaged cloud locations. DSPM (Data Security Posture Management) solutions identify this hidden data through visibility analysis, enabling backup and security policies to cover it.
Coming soonA multi-platform backup system with automated backup verification significantly increases data security. At the same time, separating backup system resources from production systems simplifies disaster recovery procedures and shortens RTO (Recovery Time Objective) — the time to resume operations after a failure or security incident.
Learn moreActive monitoring of backup infrastructure enables detection of viruses, malware, anomalies, and attack signatures. This gives us greater confidence that when data and system recovery is needed, the most recent backups will be functional and free from infection.
Learn moreUsing local or cloud repositories for backups with immutability features (time-locked protection against deletion, overwriting, and modification) is the best practice for protecting data against ransomware as well as human error. This is complemented by off-site backup — storing backups outside the organization's premises — which further strengthens cyber resilience.
Learn moreTechnical solutions and know-how from industry leaders




Cybercrime is now the world's third-largest economy. For organizations, this means real risk of downtime, data loss, and multi-million-dollar damages. These statistics from Verizon DBIR, Mandiant, and FBI reports show why cyber resilience is a business imperative, not an option.
From current state analysis to full cyber resilience in four steps
We examine your backup infrastructure, data protection policies, and identify security gaps.
We design a protection architecture tailored to your organization's resources, needs, and regulatory requirements.
We deploy solutions and train your IT team, ensuring operational independence.
For 3 months after deployment, we provide technical support, monitoring, and optimization of the implemented solutions.
Practical knowledge on cyber resilience, backup, and ransomware protection

How to make your backups tamper-proof, unalterable, and undeletable — resilient against malware and human error.
What if Object Storage and the backup system resided on a single appliance, with an identical standby node for failover?

We are preparing materials on NIS2 regulatory requirements and practical aspects of data protection compliance.
In just 15 minutes — or a bit longer if needed — we can advise you on how to increase your organization's ransomware resilience and how to eliminate common security gaps.
Click the booking button to be redirected to our expert's calendar where you can choose a convenient time for an online meeting.
The topics discussed are entirely up to you.